16 Mar Asia Tops Ransomware Table in Microsoft Report
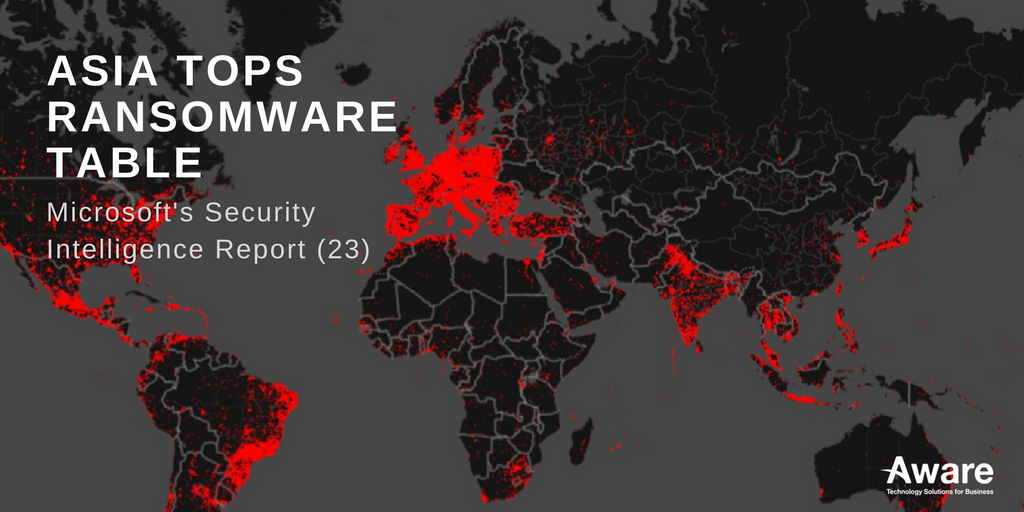
Hot off the presses, Microsoft released their bi-annual Security Intelligence Report yesterday with some interesting revelations. Most notably Asia is ranked as the highest geographical region for ransomware encounters; a prize usually reserved for Europe.
For any IT professional Microsoft Security Report is simply a must read, the analysis and depth of research is unparalleled evaluating cloud services, individual consumers, emails, and websites. In this edition, there were over 400 billion emails scanned and 18+ billion web pages scanned per month. If you haven’t had the chance to browse the report, you can grab it here.
The Big Scoop
Last year was a big deal for ransomware, WannaCry, Petya, and Bad Rabbit were some of the heavy hitters – and the ransomware theme features heavily in the report. Surprisingly, it was a relatively less well-known strain called LockScreen that actually was the most encountered ransomware. LockScreen was one of a rising trend of mobile-based ransomware viruses that have been infecting mobile and windows devices – it is expected this trend will continue.
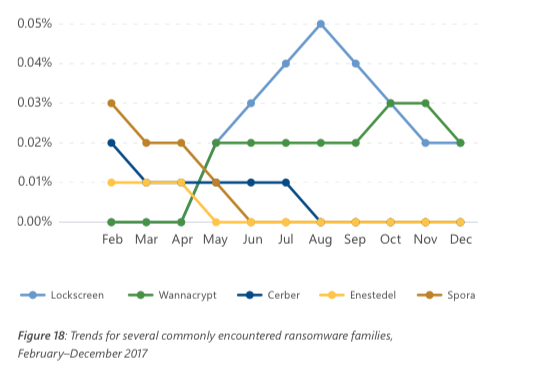
CR: Microsoft Security Intelligence Report (23)
It is not surprising that Asia witnessed high encounters of LockScreen as mobile proliferation is high throughout the continent, in particular, Thailand (around 110%) and as such the likelihood of encounters and infections is likely to be higher. Outside of ransomware activity, the report looks at the aftermath of Gamarue as well as up-and-coming trends in the digital world.
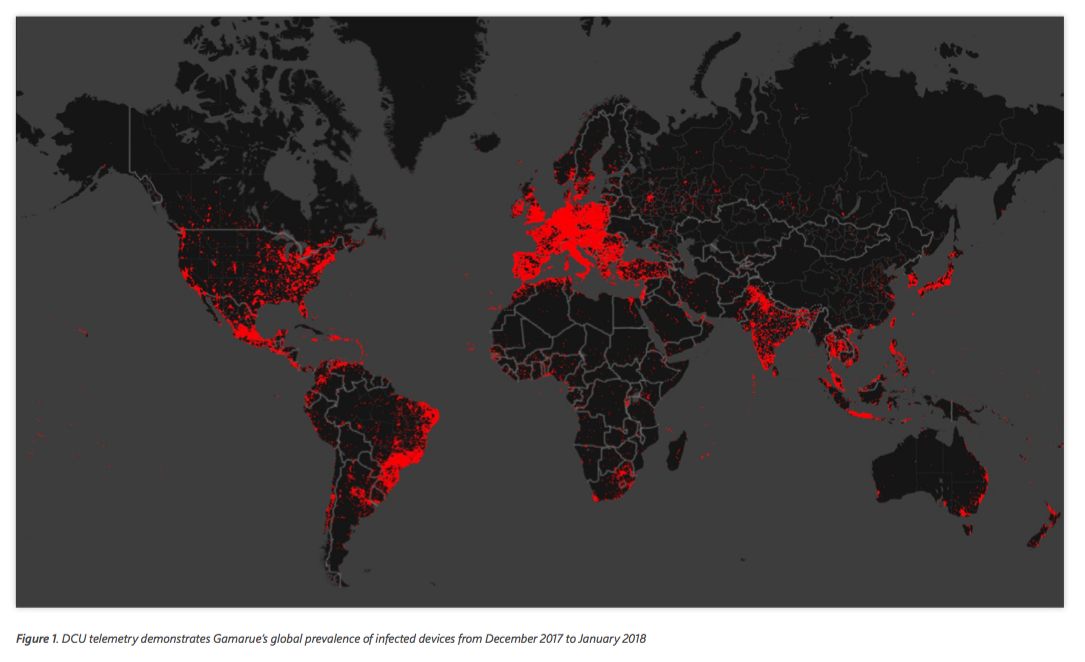
You can see Gamarue’s prevalence outlined below between December 2017 and January 2018 – Thailand is one of the high infection areas. Gamarue is mentioned in a previous Aware article, essentially it’s a botnet that can be purchased as a crime kit. The functionality of Gamarue is modular and can be extended by plug-ins which can cost extra depending on the facility, a Keylogger is $150, Teamviewer $250 but a Rootkit comes inbuilt.
CR: Microsoft Security Intelligence Report (23)
There is a move from hackers to target low hanging fruit through poorly secured cloud apps and software. Phishing remains among the most common method of attack as well as the easiest to distribute: low barrier entry, for example, an email sent out to thousands of potential victims and only requires one person’s credentials to be effective. To find out how to help protect yourself you can find our previous article here.
- Microsoft Copilot vs ChatGPT: Navigating the Future of AI Assistants - April 3, 2024
- Harnessing Microsoft 365 Copilot for Educational Excellence - March 21, 2024
- How Can Microsoft Copilot Help Human Resources Staff? - March 20, 2024
- Microsoft Copilot for Human Resources - March 20, 2024
- The Business Benefits of Microsoft Copilot for Marketing Professionals - February 19, 2024
- The key business benefits of Microsoft Copilot - February 19, 2024
- How To Increase Your Employee’s Productivity with Copilot for Microsoft 365 Word - February 16, 2024
- Transform with AI – Journey with Aware - November 20, 2023
- What is Edge Computing? Advantages and Disadvantages: - May 20, 2022
- SAP Business One Vs Microsoft Dynamics 365 - November 12, 2021