Ransomware is one of the most widespread and damaging threats on the internet. According to publicly available information, ransomware infection have outnumbered data breaches 7,684 to 6,013 over the past 11 years.
The use of ransomware, has been on the rise in recent times, growing 169% over 2015 alone and expanding again during the first quarter of 2016. Although most keep quiet about their exposure, there have been some high profile cases of digital extortion. In the middle of last year, a hospital in Hollywood paid out $17,000 in Bitcoins to hackers who had encrypted their files. This case is not in isolation; a Canadian university paid out $20,000 to attackers for the same reason. Earlier this year (January 28th 2017), clever hackers have also found ways to infect hotel door lock systems, smart TVs, and fridges. With the world on the cusp of self-driving cars and IOT – there appears plenty opportunity and evolution in the murky world of ransomware and hacking.
And it’s not just companies that are vulnerable – a new variety of ransomware had been bundled into Mac applications, including a popular app called Transmission, affecting personal users too. Ransomware distributors have also leached on to social conditioning and targeted chrome users, requesting users download infected font packs, to make the website they are browsing readable. Put simply, ransomware hackers are ambivalent with selection on who to attack.
The Issue
Technology has enabled these forms malware:
• Cryptocurrencies like Bitcoin offer untraceable ways of extorting companies and people.
• People spend more time on the internet and receive more emails and documents than ever before.
• IOT – The Internet of Things, everything is becoming digitalized, smartified, and interneted.
• Our propensity to hold everything we need on our computers, our phones, and our drives.
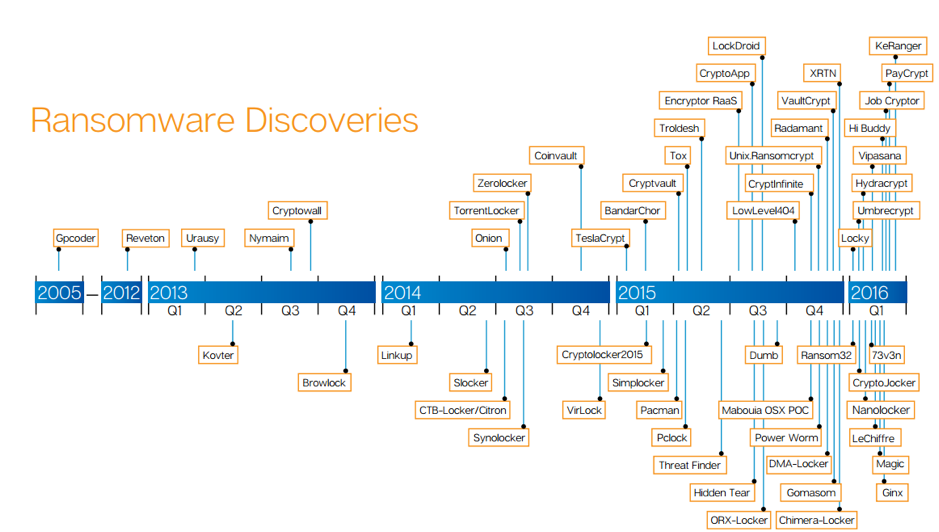
The History
Malware like this first started appearing in the late 90s, I’m sure you have come across them, Fake-AV or fake anti-virus software, a rogue, completely fake anti-virus that claimed to the hapless user that they had severe security threats on their computers, and in order to cleanse their system, they would need to pay $50.
The whole scheme was fraudulent and, over time, people became aware and skeptical of these threats. Additionally, Microsoft implemented more protections into Windows that caused previous malware attacks to be less successful (reduced administrative privileges with User Account Control). Malware writers looked for additional ways to infect computers when running with reduced permissions. Using processes that run with no administrative rights the hackers targeted the files available to the user and realized that users would pay to recover their data.
Ransomware: The first iterations
Ransomware is particularly malevolent as it imposes itself on your computer, acting as a virtual wheel clamp. The first iterations pretended to be from law enforcement and suggested the computer had been used for something illicit and that the person should pay a fine, usually around $500. The ease of online money transfer had opened a hole for hackers to get paid, much like the ease of cryptocurrency has led to anonymity.
By 2006 the Archiveus Trojan was one of the early strains which when distributed and encrypted everything in the “My Documents” directory on a system and required users to make purchases from specific web sites to obtain the password to decrypt files.
Ransomware: 2.0
The unnamed Trojan of 2011, mimicked a Window’s Product Activation notice and informed users that they must reactivate their Windows installation due to fraud. The entire sales sequence led the user down a dead end where they had to call an international number. While claiming to be free, calls were routed through a rogue operator who left callers on hold racking up large long distance call charges.
By 2013 there was 500% increase in the number of attacks between the start and end of the year. By then ransomware varieties were particularly problematic, as they imposed themselves on computers holding all files hostage. The equation was simple. Pay the money, or you cannot open your files, your pictures, your memories, your letters, your business documents, your financial documents etc. These types of viruses are particularly damaging for businesses especially when the business does not perform proper backups.
Image source: CERT-RO
Why are ransomware attacks so successful?
Ransomware is constantly innovated and highly sophisticated; hackers are continually developing new forms of ransomware to stay ahead of anti-virus programs. There is even now MaaS programs (Malware as a Service), which gives even less tech-savvy criminals a console from which to initiate attacks. Attacks are changing daily and hourly. Huge amounts of emails pretending to be purchase orders, sales requests, letters from friends etc. are being sent with the goal of just a few getting through.
Skillfully engineered emails prompt unsuspecting users to open the malware infected file. The file could be an Excel document, a Word document, a script or even just a URL to a website. Many file types can be a host for a malware infection that distributes ransomware. Once executed the malware may immediately run the ransomware code or may lie dormant for a while until it can run outside of normal business hours for maximum damage. For example you have probably received an email that enquires for a quote or sending money, with malware, they mimic this correspondence but the enclosed attachment is infected. Some highly sophisticated attackers will analyze correspondence between parties and send appropriate emails, from emails names, to receivers with titles and attachments that have a high likelihood of being opened.
Avoiding the pitfalls of a sophisticated ransomware attack is a challenge at the best of times, let alone when there are security holes and breaches at the target companies. Most companies fall foul to ransomware due to not maintaining adequate backups, delaying updates and patches, lack of security training and incorrectly implemented firewalls and safety protocol.
How does a ransomware attack happen?
There are two main ways that ransomware attack starts: via email with an infected attachment or by visiting a compromised legitimate website.
Malicious emails
This is probably the most common means of infection – where today attackers have been sending millions of emails out to businesses, almost indistinguishable from genuine ones. Usually they contain a file type that allows for code to be run. When the code is run it either immediately downloads supporting malware or it already has a ransomware payload.
Malicious Websites
Another common way is to be infected by visiting a legitimate website that has been infected with an exploit kit. Even highly popular, mainstream websites can be temporarily compromised. Exploit kits are black market tools that hackers use to exploit known or unknown vulnerabilities.
By simply clicking on a link and visiting a page you can inadvertently download ransomware files that hibernate on your computer, often with no visible sign until the damage is done.
If you feel you would like to know more about malware prevention, you can speak to our team who would be happy to assist you. You can simply mail us at: info@aware.co.th
Digital Marketing Manager at Aware Group: Working his way through the world of technology and Thailand as best as he can. Happy to contribute to other tech publications.