How Mobile App Hackers are Emptying Your Bank Account
As we fall deeper in love with our mobile devices, we are also choosing to carry and use them for more and more sensitive interactions. Reports show that bank consumers are transitioning quickly from face-to-face and online communications to banking on mobile applications bringing, with it convenience and risk in equal measure.
With an estimated 3 billion people expected to be banking online by 2021, the potential for customer engagement seems infinite, as does the potential for rogue actors and cyber criminals.
For all the potential of immediate banking services, there is also the inevitable lure for hackers looking to steal your money and access your data. More people on banking applications also means more people at risk from hackers on their mobile devices.
In order to address the ways in which hackers can access your bank accounts through mobile apps, we will share knowledge on the methods hackers use, as well as means of defense.
Cyber Criminals are notoriously industrious characters who will try to access applications and steal your data in a number of ways:
1. Mobile malware:
A thriving, evolving and growing form of malware that is designed to steal your money and your data. Mobile malware is commonly found even in the most popular applications on the most used marketplaces.
Their activities include tracking your devices, messaging your contacts, making unapproved charges and trying to access your banking information.
If you don’t have a reputable antivirus software on your mobile device, it may be time to get one. Malware and spyware can run unnoticed on your mobile device, while secretly tracking your usernames and passwords and more.
2. Man-in-the-middle:
When a banking application and the bank’s servers communicate over the internet, they verify security credentials with each other, ensuring the user is the genuine account holder and the bank has the correct security certificate.
With the “Man-in-the-middle” hack, fraudsters will usually access the same public Wi-Fi as the application user and attempt to send a fake bank server certificates to the mobile app. If your application accepts the fake certification it can enable the hackers to receive the user’s personal information.
3. Loss or Theft:
Ever increasingly we are living more on our mobile devices and we are all carrying more and more sensitive information on them. Banking apps give access to some of our most valuable information should they fall into the wrong hands. This is problematic both if your device is lost or stolen, but also if you are reselling.
If you are selling off old tech, make sure you wipe and restore the device — you don’t want private data being on your phone when someone else is using it.
4. Poor Internet Safety Protocol:
Our increasing reliance on mobile devices has not been matched by our increasing standards in security on them. According to Symantec less than 50% take basic security precautions like install security software, or back up mobile devices. 57% of the population don’t even know that security software existed for mobile devices.
5. Key logger software:
As it says on the tin, key logger software is found on computers and phones. They are designed to secretly record a person’s actions as he or she uses the device. With a banking app tracker, the malicious software could log your usernames, passwords and account details and send them to bad actors.
6. Phishing:
A tried and true method for criminals the world over. More commonly found in email scams, but works just as well with applications. Essentially criminals send the user messages pretending to be banking institutions, hoping to coax sensitive information from users.
7. Data Leakage:
Your mobile applications and the permissions you have granted them are often sweeping. Riskware apps pose a threat to mobile users who haven’t been proactive in their security. Typically, ‘free’ apps found in official marketplaces generate revenue by advertising or selling your information.
Data leakage can also happen when apps are infected with malicious code, allowing hackers back door entry to your phone and your data. This has even happened on popular applications found on Google Play and Apple Store.
8. Improper Session Handling:
To facilitate better user experiences, mobile applications use “tokens” when interfacing with external programs.
This process enables the bank to authenticate the identity of the device, like passwords on a website. While you are logged in you will be able to utilize full functionality because tokens keep authorizing your interactions.
Secure applications generate a unique code for each session, however, improper session handling happens gives malicious actors your session token information and allowing them to impersonate you and interact with your bank masquerading as you possibly transferring money or emptying your account.
9. Network Spoofing:
This is one we should ALL be careful to watch out for. Network spoofing is the creation of fake connections that look like Wi-Fi networks, from reputable companies but are actually traps. They can usually be found in high traffic areas such as coffee shops, libraries, and airports. The hackers give their own connections the names of reputable brand names and require users to create a free account on the spoofed network in order to access the WiFi.
The first instance of hacking can occur when users enter usernames and passwords to “log-in”, often times people use the same email and password over and over again, giving hackers the opportunity to try other websites — the second opportunity for hackers is that now you are logged in, to what you believed to be a reputable network.
10. Any Application Could be a Risk:
Throughout 2017, 100s of apps have been pulled from Google Play and Apple App Store for security reasons. Both marketplaces have fallen victim to malware and adware in some of their most popular applications. McAfee found that of 150M applications that we scanned, around 9 million had malware with 3 million devices infected in a 6-month period.
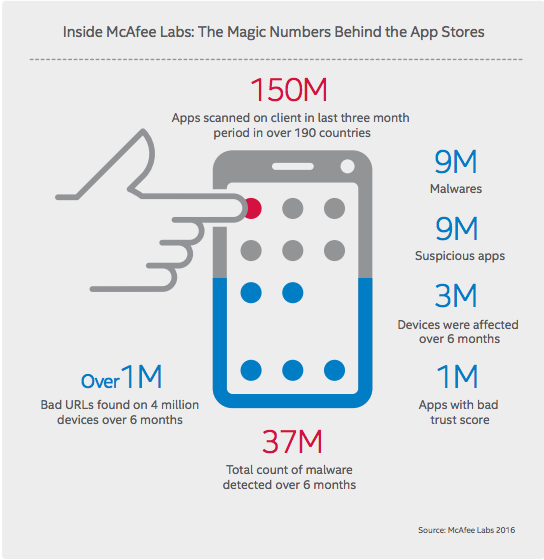
Source: McAfee Labs
The more time we spend on mobile devices, combined with the more sensitive interactions we have, should directly correlate to using increased security. It just now appears that mobile app developers, as well as users, don’t take the necessary safety precautions. If you would like to develop a secure mobile application or find out how you can secure your current applications contact Aware today.
Digital Marketing Manager at Aware Group: Working his way through the world of technology and Thailand as best as he can. Happy to contribute to other tech publications.